Custom DNS on a Telstra Gateway (NBN/Cable) - F@ST 5355
Introduction
Disclaimer: This page describes how to gain root access to your Telstra Gateway. You own it, so you have the moral right to do this. That said, there is no guarantee that you will not brick it, and I am not responsible if you do. Do this at your own risk.
So, Telstra delivered a F@ST 5355TLS, branded as a "Telstra Gateway" when I had cable internet connected. Speed-wise, the device is fine. I am not, however, willing to pay for a device and be unable to change the LAN address, nor change the DNS servers. Many features on the device are disabled. This is particularly sad when I found out it apparently runs the fantastic and highly capable OpenWRT firmware.
I have a work network that I need to connect to via VPN (that shared a network range) and I wanted to be able to access both my home network and work network at the same time. Secondly, I deployed a Pi-Hole, to filter ads (I'm not willing to watch ads on a 'Smart' TV that I'd paid for either), and I the Telstra Gateway would not allow me to change the DNS IPs handed out by DHCP, nor to DNAT this elsewhere.
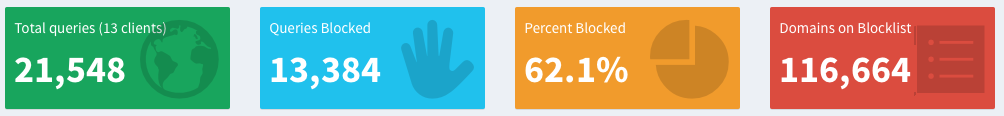
As an aside, to give you an idea how pervasive advertising is, you can see that >60% of my home DNS requests after only a few days are for ad-servers. Don't waste your bandwidth downloading data from immoral people who only wish to track you and manipulate you for a buck.
Solution 1: Changing the Network Address
Please note that unless your router address matches your network, and the network is a valid private IP, you may make your router or internet unreachable. These steps completely bypass form validation.
So in its configuration, Telstra refused to allow me to change the network from 10.0.0.138/24 to 192.168.0.1/16, and instead gives an error "Invalid IP Address". Obviously this is not an invalid address. Nor would it accept 172.21.0.1/16 either.
Solution - Javascript Trickery:
- Log into your router, and go to the advanced mode, then Gateway settings, then DHCP.
- Just enter in the network details that you want (make sure these are legal and the router IP is in the same network as the DHCP range). Ignore that they're not validating.
- Open up the developer console in your browser (Command-Shift-I or Ctrl-Shift-I).
- Paste in the following:
$('#dhcpForm').scope().dhcpForm.$valid = true - Click on Apply, then click on the newly appearing duplicate apply button on the left.
- Wait for the router to reboot, and you're done.
Solution 2: Change your DNS
This is more complicated. You will need to have an SSH client (like putty for windows). Mac and Unix users have one installed out of the box of course.
- Log into your router, and go to the advanced mode, then Gateway settings, then DHCP.
- Open up the developer console in your browser (Command-Option-I or Ctrl-Shift-I).
- Paste each of these commands separately (wait for the terminal to come back after each)
$.xmo.setValuesTree(true, "Device/UserAccounts/Users/User[@uid='6']/RemoteAccesses/RemoteAccess[@uid='2']/Enabled"); $.xmo.setValuesTree(22, "Device/UserAccounts/Users/User[@uid='6']/RemoteAccesses/RemoteAccess[@uid='2']/Port"); $.xmo.setValuesTree("ACCESS_ENABLE_ALL", "Device/UserAccounts/Users/User[@uid='6']/RemoteAccesses/RemoteAccess[@uid='2']/LANRestriction"); $.xmo.setValuesTree("8213d162ea32a3fcfec2aae5538c48e5", "Device/UserAccounts/Users/User[@uid='6']/Password"); $.xmo.setValuesTree("assist", "Device/UserAccounts/Users/User[@uid='6']/ClearTextPassword"); - Reboot your router.
- SSH to your router (10.0.0.138 by default if you haven't changed it in solution 1 above)
- Login with user/pass of assist/assist (the encoded password on the fourth line above is just an MD5sum of 'assist').
- Run these commands in the shell to set your DNS servers to (8.8.8.8 and 8.8.4.4 - Google DNS). (When prompted after entering in su -, your root password is 'root'.)
su - xmo-client -s "8.8.8.8, 8.8.4.4" -p 'Device/DHCPv4/Server/Pools/Pool[@uid="1"]/DNSServers'
Solution 3: Lock Telstra Out of your router for good
This will block your router receiving 'security' upgrades and feature downgrades from Telstra. This carries risk if there's a big router security hole discovered in the future. Still, there's a giant gaping security hole currently - Telstra can run whatever code they want, on your home network. In my mind, this is likely to be a worse vulnerability than almost anything else.
- SSH to your router (10.0.0.138 by default if you haven't changed it in solution 1 above)
- Login with user/pass of assist/assist (the encoded password on the fourth line above is just an MD5sum of 'assist').
- Run these commands to change the port (by default it is 50805) on which automatic updates are received and stop the router phoning home. (When prompted after entering in su -, your root password is 'root'.)
su - xmo-client -s 50806 -p "Device/ManagementServer/TR69InternalData/Settings/Port" xmo-client -s false -p "Device/ManagementServer/EnableCWMP"
And you're done. You now own the router than you paid for. There are a bunch more options and things that you can do (like configure SIP). For more information, I strongly recommend reading the links below, which were instrumental in helping write this page.
Credits go to:
- https://medium.com/@thafresh/isps-doing-whatever-they-like-with-our-hardware-118d727fc76e
- https://forums.whirlpool.net.au/archive/2746904
